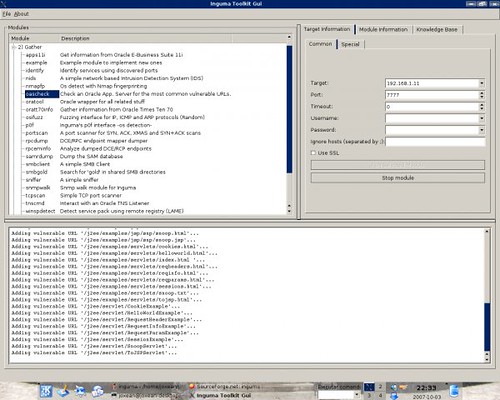
Quite a few people seem to be interested in this tool, so here is the latest revision - Inguma 0.0.6.
For those that don’t know, Inguma is a free penetration testing and vulnerability discovery toolkit entirely written in python. Framework includes modules to discover hosts, gather information about, fuzz targets, brute force usernames and passwords, exploits, and a disassembler.
In this new version various things have been added like new modules and improvements in the existing ones. For example the Oracle modules. The Oracle payloads now uses the Cursor Injection method when possible so CREATE PROCEDURE system privilege is not needed to become DBA.
The support for InlineEgg, added in version 0.0.5.1, have been removed and a new completely free library have been added (PyShellCodeLib).
The static analysis framework OpenDis have been enhanced and now you can use the API exposed by OpenDis to write your own binary static analysis tools. As an example of the API, a tool to make binary diffs have been added. Take a look to the file $INGUMA_DIR/dis/asmdiff.py and to the README stored in the same directory.
New 5 exploits for Oracle Databases have been added and the module “sidguess” have been enhanced to retrieve the SID of the database instance from the Enterprise Manager/Database Control banner when possible.
The new modules added to the discover, gather and brute sections are the following:
- brutehttp: A brute forcer for HTTP servers.
- extip : A tool to known your external IP address. Very useful to check anonymous proxies.
- nmbstat : A tool to gather NetBIOS information.
- ipscan : A tool to make IP protocol scans. The tool check what IP protocols are enabled in the target.
- arppoison: A tool to poison target’s ARP cache
You can download Inguma 0.0.6 here:
Or read more here




No comments:
Post a Comment